This guide provides examples of ways to recognise a possible phishing email. The list is not exhaustive and any or all of the steps may apply.
This is an example of a phishing email sent to a University of Derby account. The links in the description below navigate back to the image.
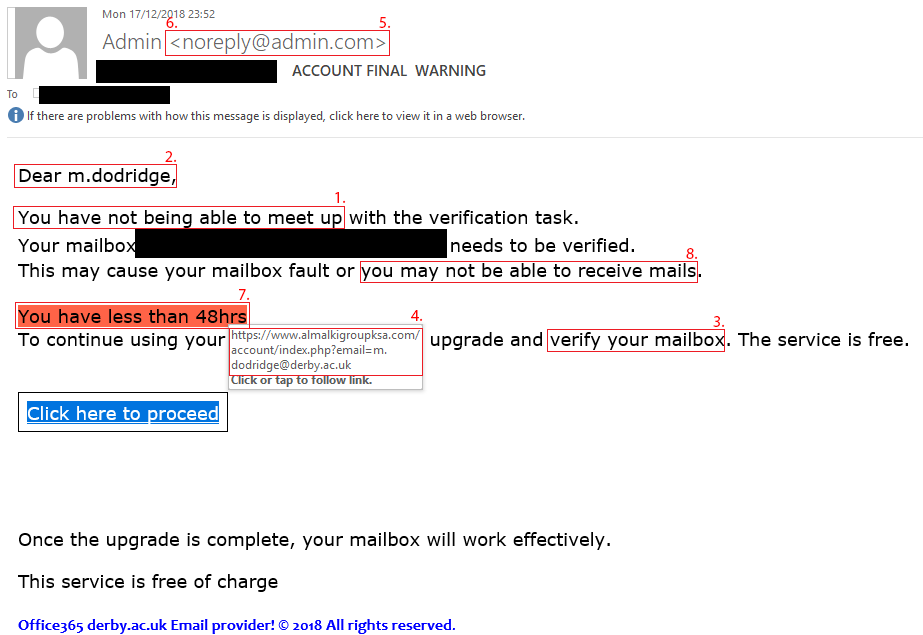
- The email contains poor spelling and/or grammar. Phishing emails may contain poor spelling and grammar. Also look out for inconsistencies in the presentation of the email (e.g. the email may contain various font styles, font sizes and mismatched branding);
- The email contains an impersonal greeting. Phishing emails will often contain greetings such as “Hi”, “Hi <email address>”, or “Dear Customer”;
- The email asks for your personal information. Nobody at the University of Derby will ask for your sensitive information (e.g. personally identifiable data, usernames and passwords, or banking information) by email or by phone;
- The email contains a mismatched URL. Phishing emails often contain embedded links disguised as legitimate websites. Those embedded links probably won’t direct you where you’d expect it to. If it looks suspicious, hover your mouse over the top of the link to check if the hyperlinked address matches the one in the email;
- The email contains a misleading domain (e.g. derby.ac.uk) name. Malicious actors often attempt to ‘spoof’ legitimate domain names to give the impression that embedded links will direct to legitimate websites. For example, staff.derby.ac.uk is a legitimate link to the University of Derby’s domain, whereas derby.maliciousurl.com is not;
- The email contains an unusual ‘from’ address. Malicious actors often attempt to ‘spoof’ legitimate email addresses to give the impression that the email is being sent from a legitimate organisation. This tactic often hides unusual email addresses behind what appears to be a genuine sender name. If the email looks suspicious, hover your mouse over the sender name to see the email address from which the email was sent;
- The email creates a sense of urgency. Phishing emails may attempt to create urgency by warning you your Office365 account may expire or that your account has been compromised to encourage you to take immediate action;
- The email contains unrealistic threats. Similarly, phishing emails may also attempt to create urgency by using intimidation to scare victims into disclosing sensitive information or making a payment.